Two weeks ago Microsoft announced the availability of Intune/ Azure AD Conditional for macOS in this blog article. With this feature it is possible to only allow access to your Azure AD applications to compliant macOS devices and block access to all other macOS devices. Around the same time Microsoft released the Intune Company portal app for macOS in preview. Before this app you needed to enroll your Mac devices via the Intune web portal.
In this blog I will show you how this works with an example of blocking non-complaint macOS devices access to Exchange Online. But off-course it is possible to block access to all the other applications in your Azure AD.
Setup the macOS Conditional Access Policy
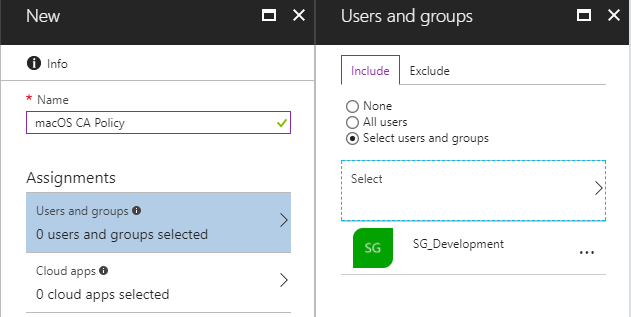
Open up the Azure portal, go to Intune and on the Conditional Access tab click New Policy. First we need to set the assignments; to which group of users this policy needs to be enforced, what application we want to control access to and under which conditions. Under Users and group select the user group the policy needs to be assigned to.
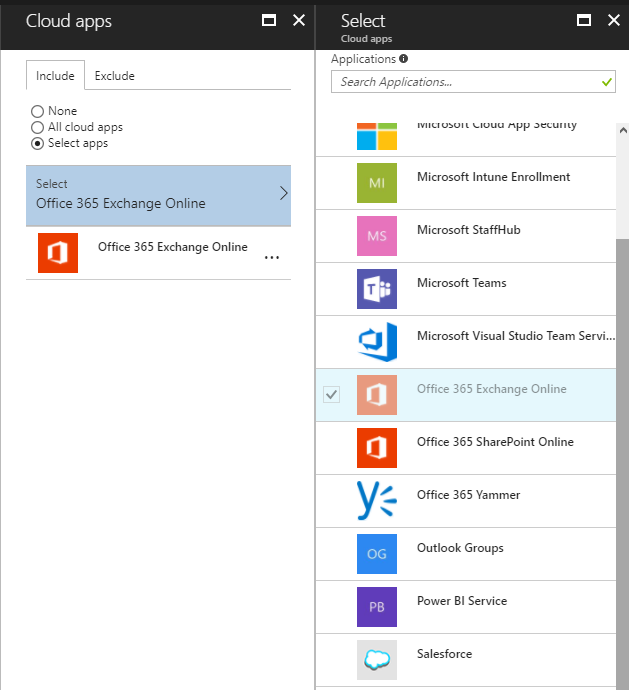
Select your applications, I only selected Exchange Online.
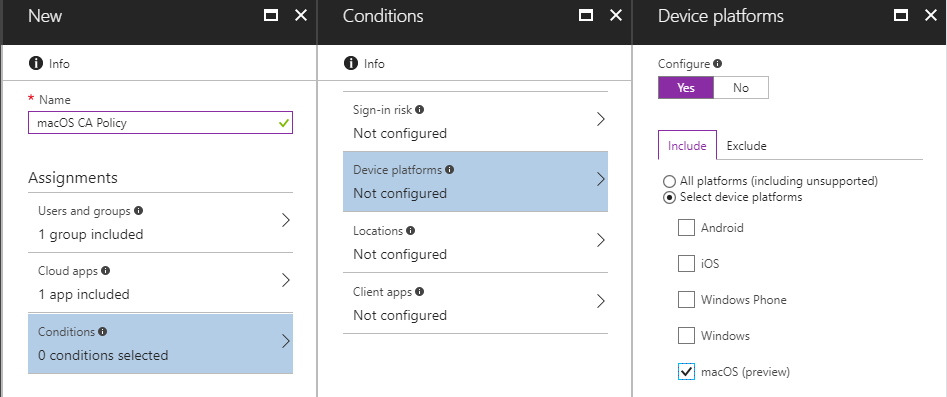
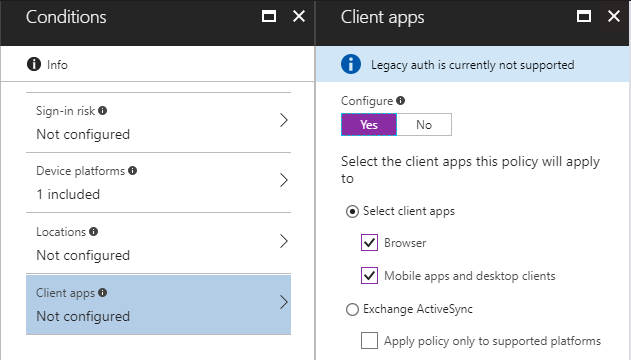
Now choose the device platform. You can select every platform separate or select All platforms, so even unsupported platforms are targeted.
On the client apps tab you can choose if you only want to target browsers (for OWA in my case), client and desktops apps or both. I mostly prefer to block the browser and apps.
I want to allow access to Exchange Online only from Intune complaint apps. But you can also require other controls like MFA or a combination of controls.

After all settings are set, don`t forget to Enable the policy, by default it is turned off.
Enrolling the macOS device to Intune
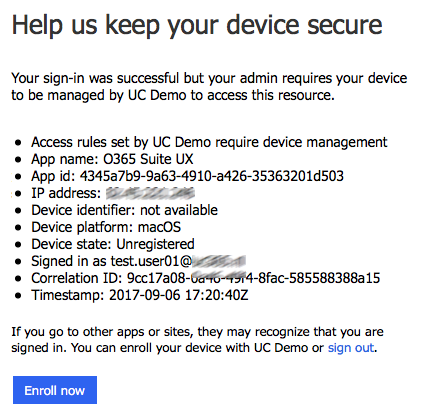
Now let`s have a look at the Mac. When we sign-in to Outlook, that is successful, but because this device isn`t enrolled to Intune, it is unknown if this device is complaint and you are asked to enroll your device. When you click on the Enroll now button you are redirected to the download page of the new Intune Company Portal app for macOS.
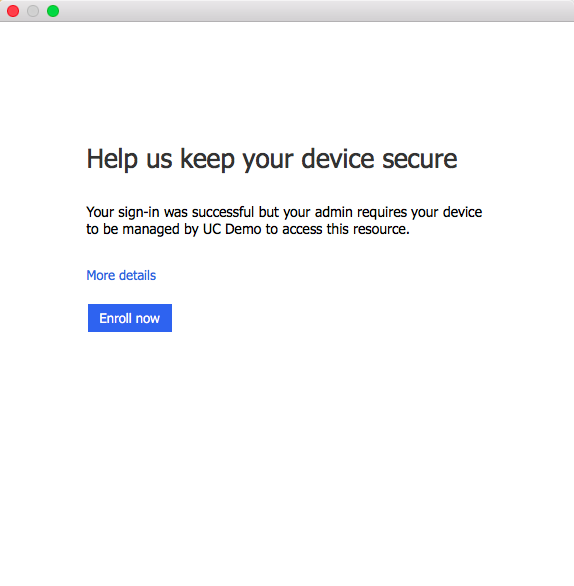
When you try to logon to your mailbox via a browser on a non-compliant macOS device access is blocked.
After downloading and installing the Intune app, you need to sign-in to the app. You will see the familiar logon page like sign-in on to the Office 365 portal.
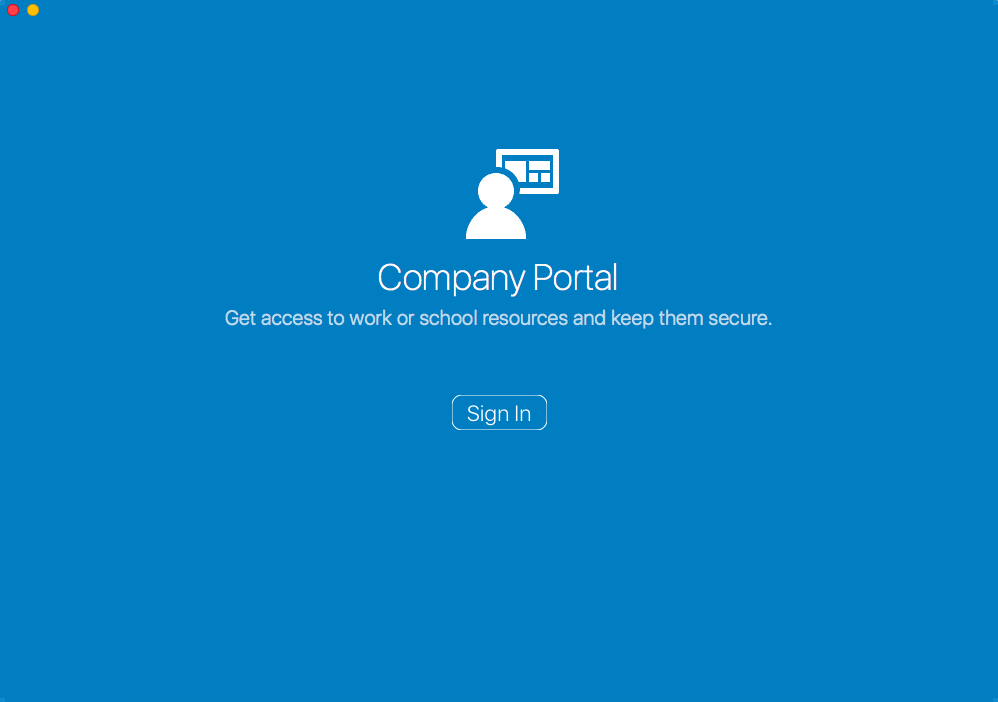
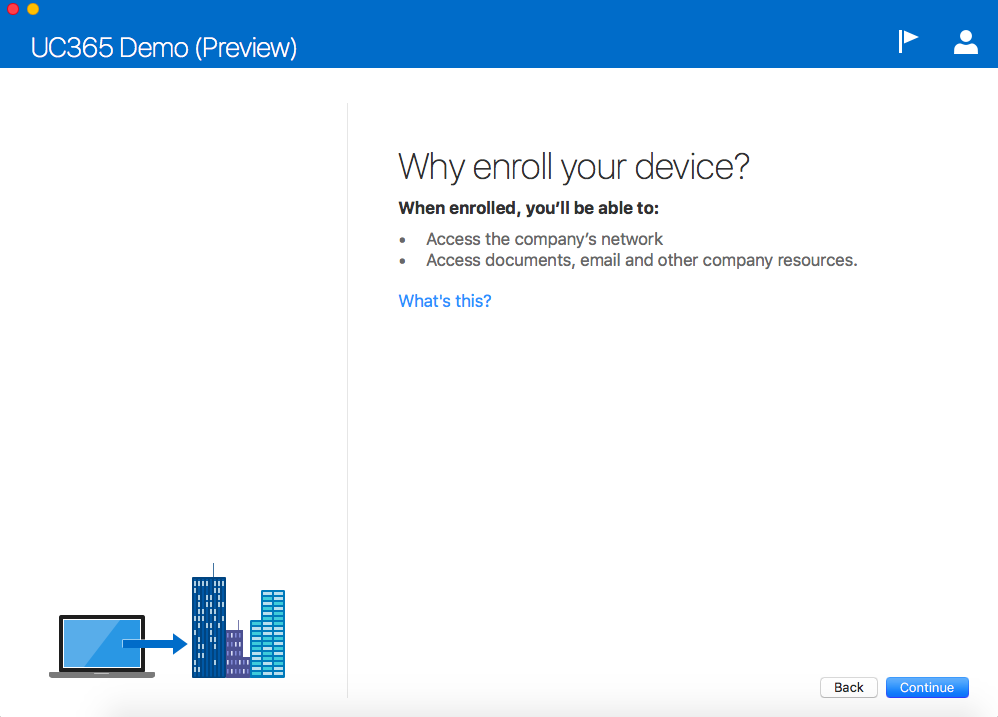
Now we need to go on with the enrollment process like it is with mobile devices enrolling to Intune.

You will be informed why you need to enroll your device.
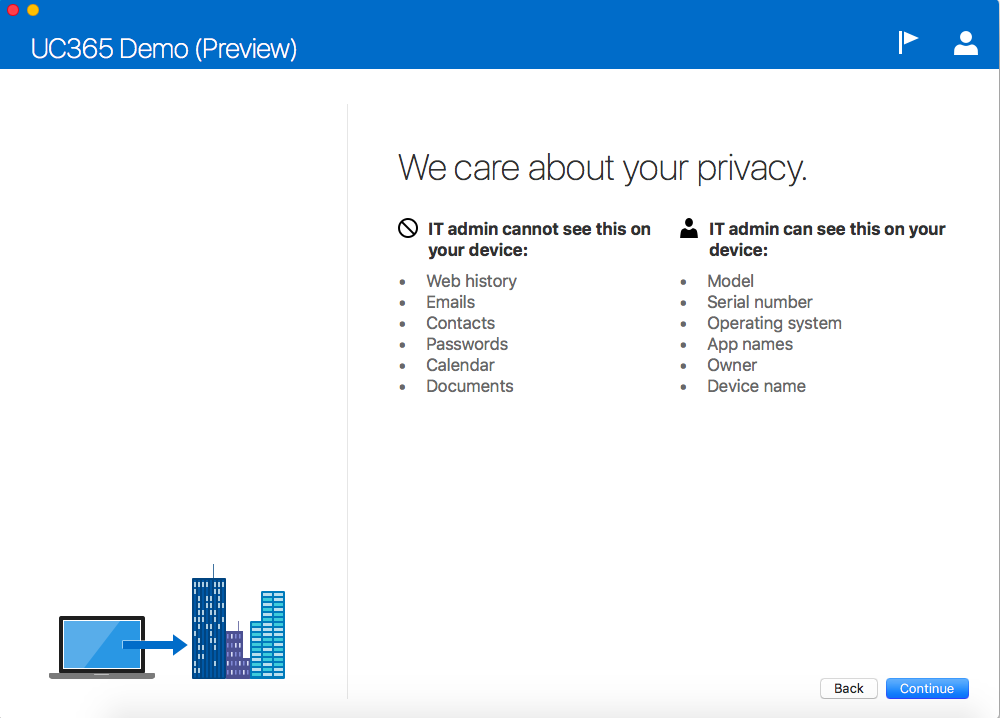
You get information about your privacy, what can the IT admin not see from your device and what information can the IT admin see from your device.
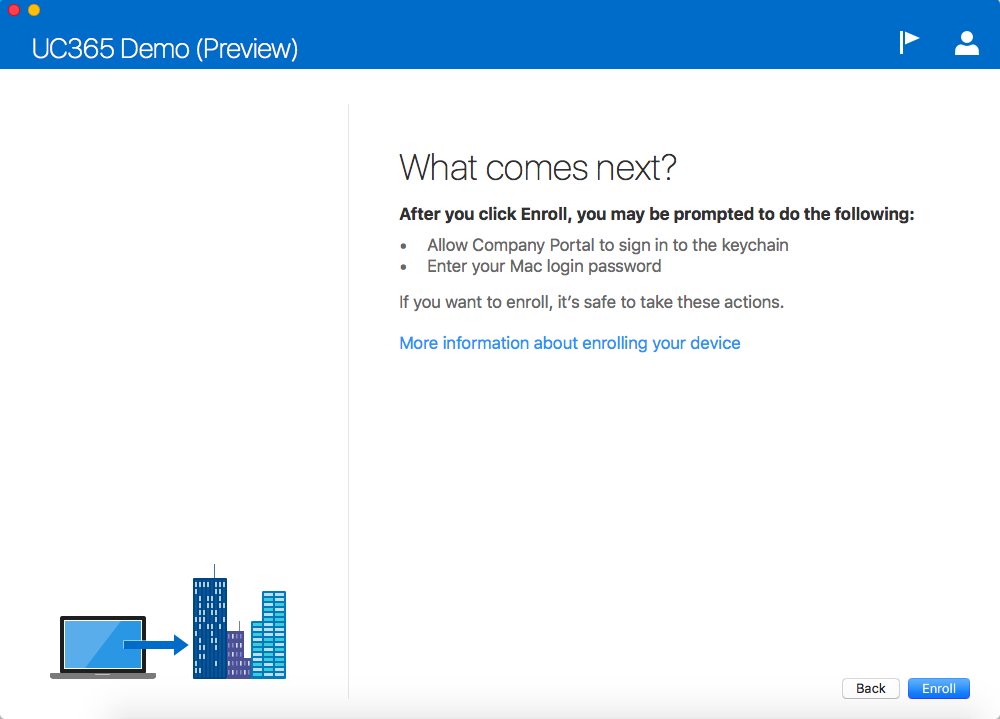
You get information what you van expect during the enrollment.
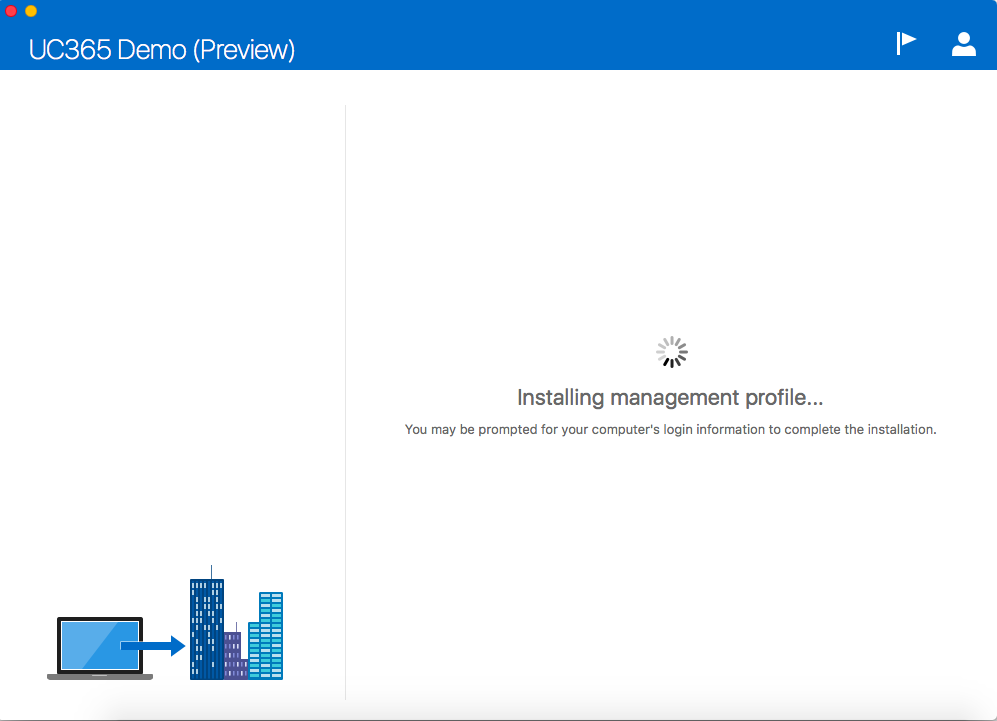
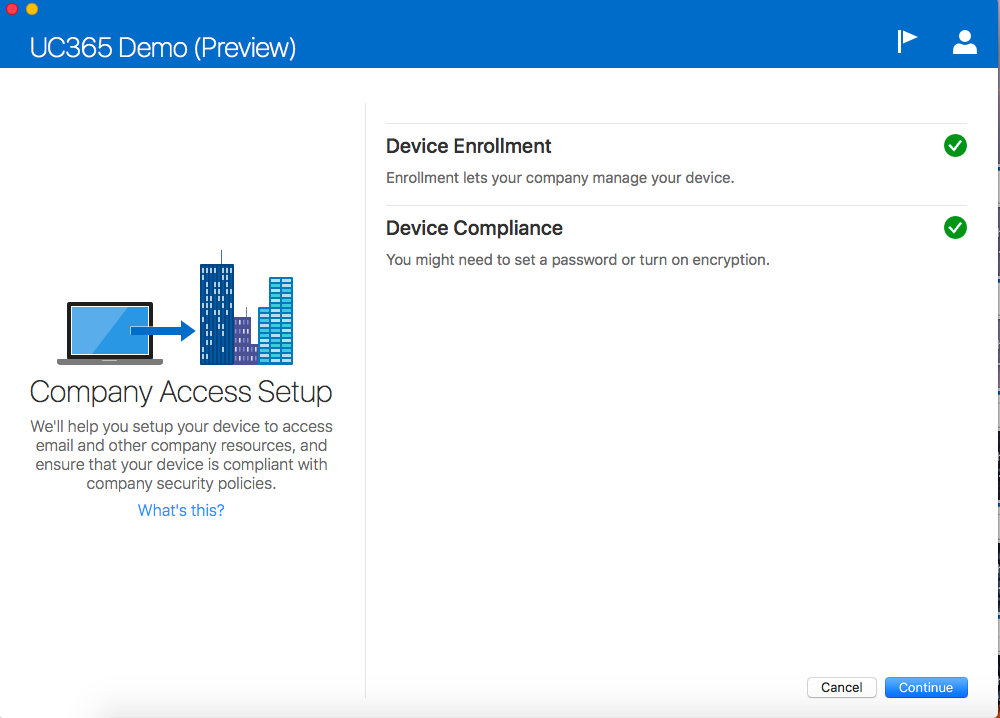
Your device is enrolling to Intune; installing a management profile and deploying other settings you set in Intune.
After enrolling the device and when the device is compliant you are finished.

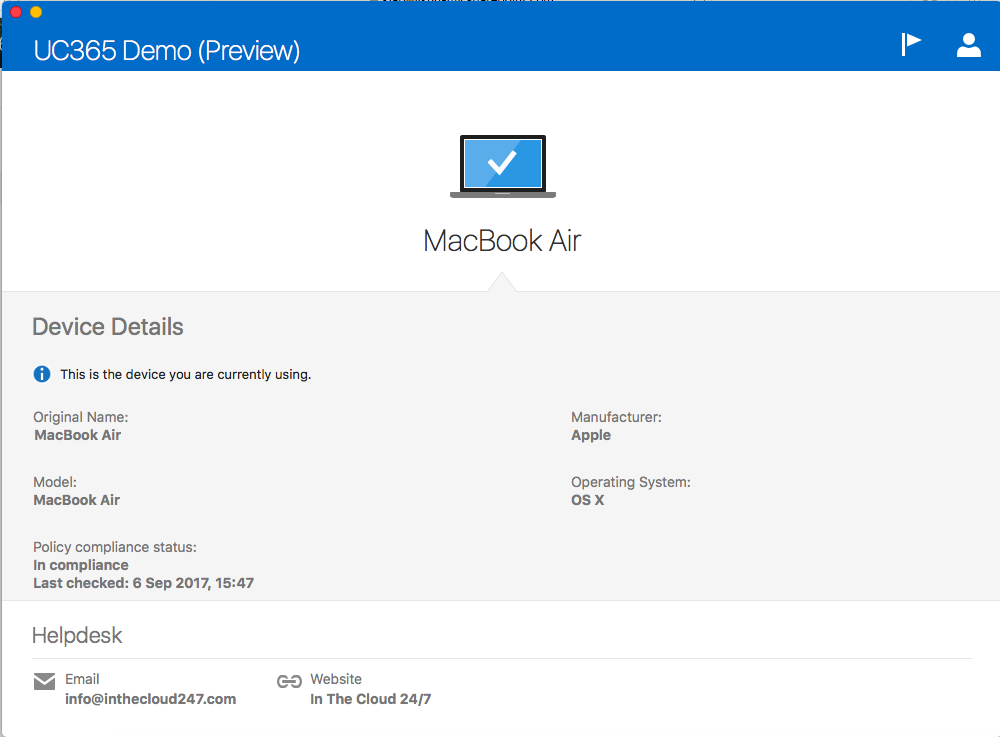
When you are done you get an overview screen with information about your device, like if it is compliant or not and last sync time. But if your IT admin filled in information about the helpdesk like the email address and website, it is shown at this page.
When your macOS device is enrolled in Intune and when it is compliant, you are allowed to sign-in to your webmail and to get access to your email via the Outlook client.