Imagine you just joined a company. As you`re working from home, a Windows 10 laptop and a mobile phone are dropped at your house. You received a new user account, but you didn’t receive a password. Instead of that, you received a FIDO2 security key and a Temporary Access code.
Setup of your new account without using a password sounds like the future. But since the preview of Temporary Access Pass, on which I published an article yesterday, this isn’t the future anymore, this is the present!
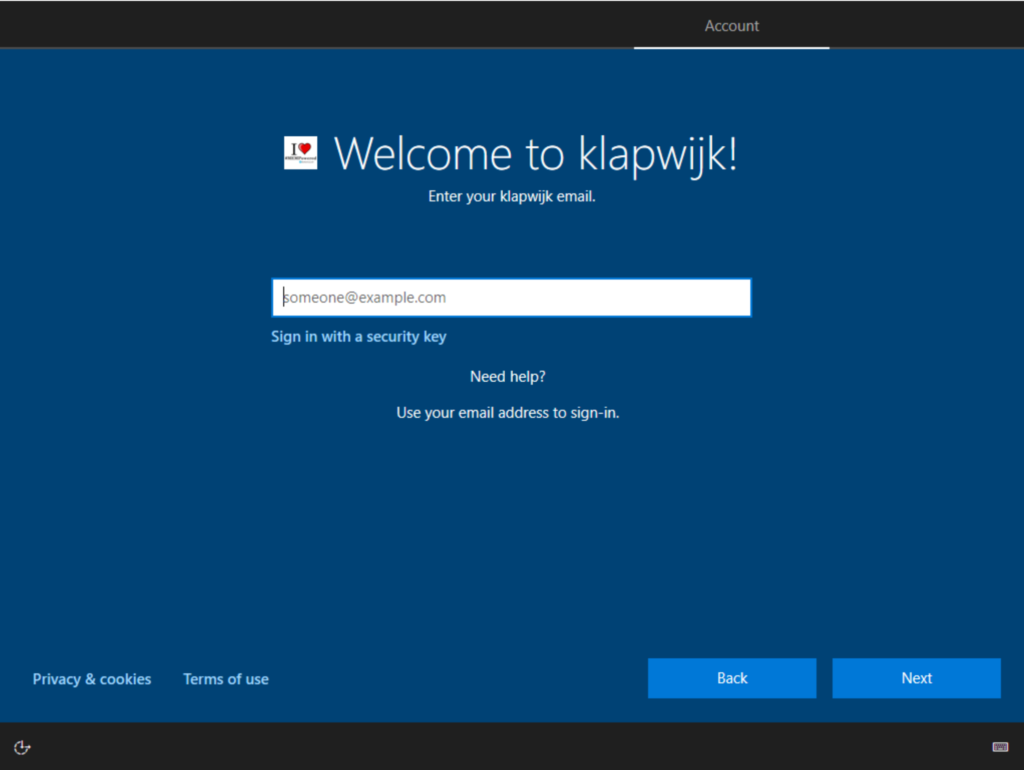
Where I used the Temporary Access Pass (TAP) to authenticate for Windows Autopilot enrollment in the previous post, this week another option to authenticate popped up on one of my test devices. On the sign-in screen from my Windows 20H2 device “Sign in with a security key” showed up.
So we can also use the TAP to set up our account via the My Security Info page and when that is finished, register our FIDO2 security key. Ok, this works best when you already have a Windows 10 device, but for this post I assume we have one 🙂
Now that we have set up our FIDO2 key, we can use it to start our Windows Autopilot enrollment!
So we start our Windows Autopilot registered device and choose Sign in with a security key.
On the next page, a new pop-up is shown, which asks to Insert your security key into the USB port.
As soon as this is done, touch the key (and enter the PIN if you`re not using a bio version).
If multiple accounts are stored on the key, this pop-up is shown to select the correct account.
And the Windows Autopilot enrollment begins!
When the enrollment is finished, we use the FIDO2 key to sign-in to Windows.
And here a short video of the enrollment.
Sign in with a security key and Temporary Access Pass are pretty cool developments if you ask up me!
Thanks for reading this post and happy testing!
And if you’re interested in more passwordless related articles have a look at this overview.